Navigating Cloud Security: Valuable Insights from Google Cloud Security Posture Reviews
Chief Growth Officer
Do you know if your Google Cloud platform's security posture is up to date? Gapps' Google Cloud Security Posture Review sheds light on the challenges in cloud security and provides concrete action recommendations, and a roadmap for improving platform security. Based on the latest cloud security audits, we've compiled the challenges organizations face in managing cloud platform security.

Is your Google Cloud platform's security posture adequate?
Have you ever found yourself tossing and turning at night, pondering the complexities of cloud security? If your answer is ’yes’, fear not – we have all been there. In fact, here at Gapps, we have recently had our own cloud security adventure, diving pretty deep into the topic of keeping digital spaces safe and sound. On this specific adventure, we conducted Google Cloud Security Posture Reviews together with more than 20 clients, and made some truly eye-opening discoveries!
Before we get into the juicy details of the matter, however, you might be wondering what a Google Cloud Security Posture Review is exactly? To put it simply, it's a comprehensive assessment of your cloud environment's security position. From identity and access management to data protection and compliance, a Google Cloud Posture Review leaves no stone unturned in ensuring your cloud infrastructure is protected against potential cyber threats.
But why should any of this matter to you, you ask? Allow us to explain: in today's digital landscape, where cyber threats are constantly increasing, safeguarding your data and assets needs to be taken seriously. This is where we at Gapps come in!
What are the most common challenges of cloud platform security?
Remember those Security Posture Reviews we mentioned having conducted earlier? Our Google Cloud Security Posture Review model combines automated tools for auditing Google Cloud security configurations with good old-fashioned human expertise. We conducted a total of 22 assessments, ranging from small startups to experienced publicly traded companies.
And what is it we found out? Let's break it down by area! Here is what we came across:- Cloud Resource Management: No separate projects for test/qa/prod; organizational policies not in use; and projects/resources that are not created automatically (IaC / Terraform/Pulumi).
- VM Security: The updating of operating systems is not automated or scheduled; server-level logs are not exported anywhere; and server service accounts have excessive permissions (Default Compute Engine SA).
- Network Security: Default networks and default network-generated open firewall rules in use; network traffic and firewall rules are not logged; WAF/DDoS protections not in use; and remote connections do not use Zero Trust features.
- IAM: Users have excessive permissions (Owner/Editor); MFA is not enabled on accounts; and user lifecycle management is not automated (provisioning/deprovisioning)
- GKE: Excessive permissions on Service Accounts; public IP addresses; and GKE Control Plane's public endpoint is not blocked or protected by an Allowlist
- K8s Security: Inter-pod traffic is not restricted by Network Policy; security policies are not enforced on workloads (e.g., Gatekeeper); and vulnerabilities in images are not monitored.
- Data Protection: Service Accounts keys lack rotation model or automation; publicly exposed Cloud Storage buckets; Cloud SQL instances with public addresses and without enforced encryption in connections.
- Security Operations: Insufficient logging; unnoticed misconfigurations; and no capabilities to detect suspicious activity from logs
Our recommendations based on the insights
Sounds like a whole lot, doesn’t it? Contrary to what you might believe right now, we’re not just here to point out the problems – we’re actually more about providing solutions. So, based on our findings, we've put together a few recommendations to strengthen your cloud fortress:
- Build secure foundations: Strengthen your cloud platform's security base and level up your expertise.
- Reduce attack surface: Minimize vulnerabilities and boost your defenses against external threats.
- Implement CSPM: Embrace Cloud Security Posture Management and keep a keen eye on your cloud's security posture.
- Shift left for security: Insert security practices early in your development pipeline and nip vulnerabilities in the bud.
Ready to level up your cloud security game?
Why not partner with us at Gapps for your next Security Posture Review and take the first step toward a safer, more secure cloud environment? Check out our services right here and let's tackle the cloud together! Until next time, stay secure, stay savvy, and keep riding the cloud!
>> Get your Google Cloud security in shape with Gapps' Security Posture Review!
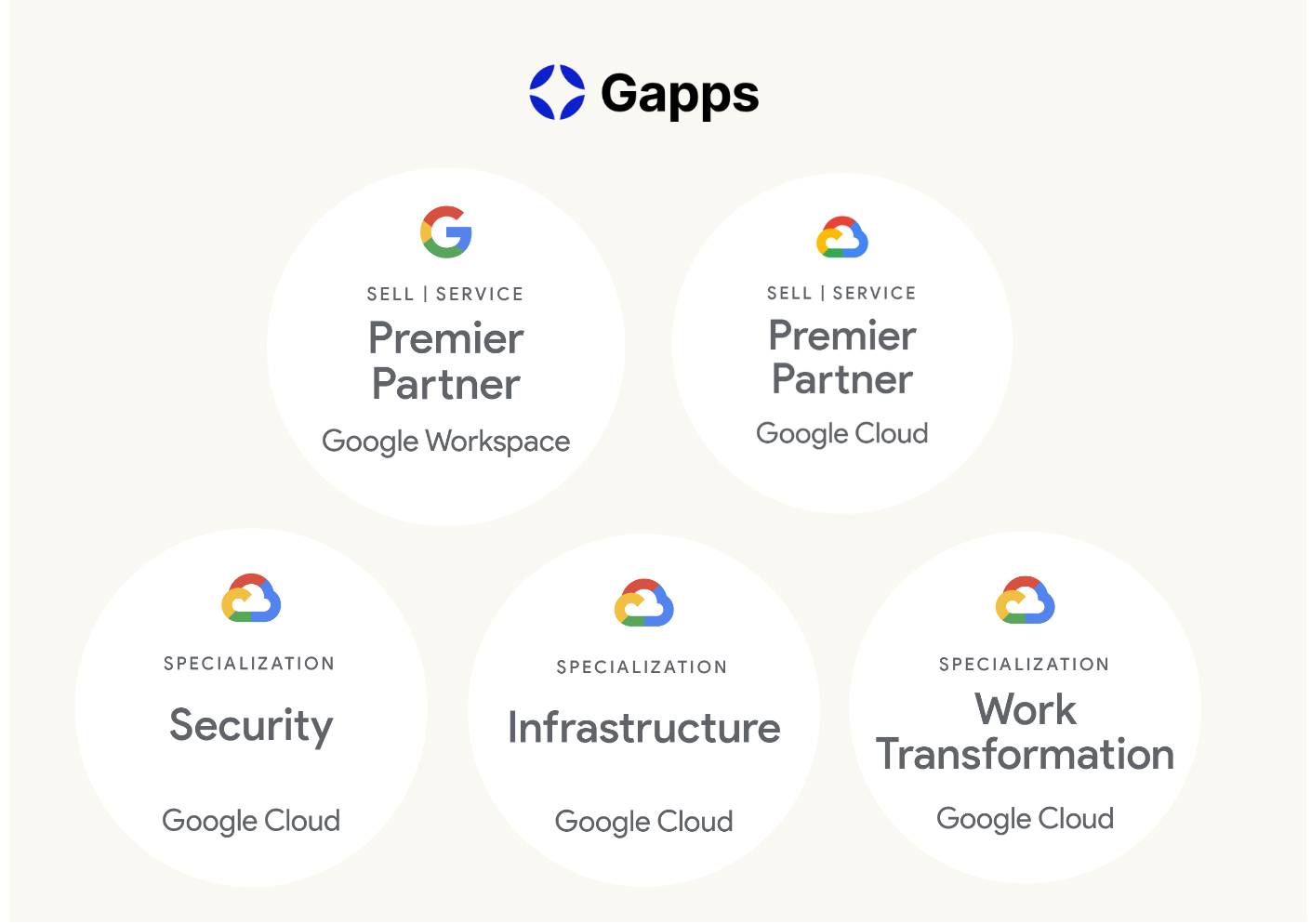
Why Gapps?
Gapps is a Finnish IT consultancy company offering a wide range of cloud services and consulting services to businesses in various industries in the Nordics. Gapps is known for its technical expertise, customer-focused strategies, and high-quality customer support related to Google products.